Advanced Privacy
Secure Your Data

Vault Protection
Data Protection
Protect Your Files
Secure Messaging
Encrypted Storage
Secure Your Privacy
Works only with Microsoft Windows 64 bit
-
Advanced Privacy Software Suite
$29.99 -
PC lock
$5.00

How StealthLock Protects Your Data
Privacy doesn’t stop at messaging and storage; StealthLock includes vault protection to
safeguard your digital assets. This feature creates a secure area on your device where
sensitive files can be stored away from unwanted access. Moreover, the tamper-proof
self-destruct system acts as a fail-safe, ensuring that any data falls into the wrong
hands is permanently deleted. By integrating these innovative protective measures,
StealthLock makes it harder for hackers and unauthorized users to compromise your
information.
In summary, StealthLock offers a holistic approach to privacy, providing users with the
tools necessary to keep their digital presence secure. Whether you’re looking to
maintain confidentiality in your communications or safeguard your critical files,
StealthLock stands out as an invaluable resource in today’s digital landscape.
Stealth Lock — The Ultimate Data Protection System
Your Data. Your Control. Forever.
In a world where your files are constantly at risk from hackers, corporate spying, and even accidental loss, Stealth Lock is your ultimate shield. Designed for absolute privacy and uncompromising security, this is not another “cloud service” that can be hacked or subpoenaed — your data stays with YOU.
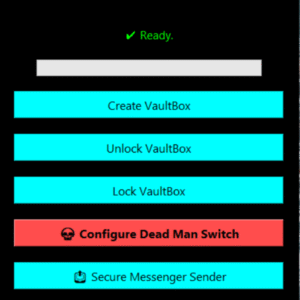
Unbreakable VaultBox
- Encrypt and lock your most important files in seconds.
- One password unlocks your vault — lose it and no one (not even us) can open it.
- Works with documents, photos, videos, and entire folders.
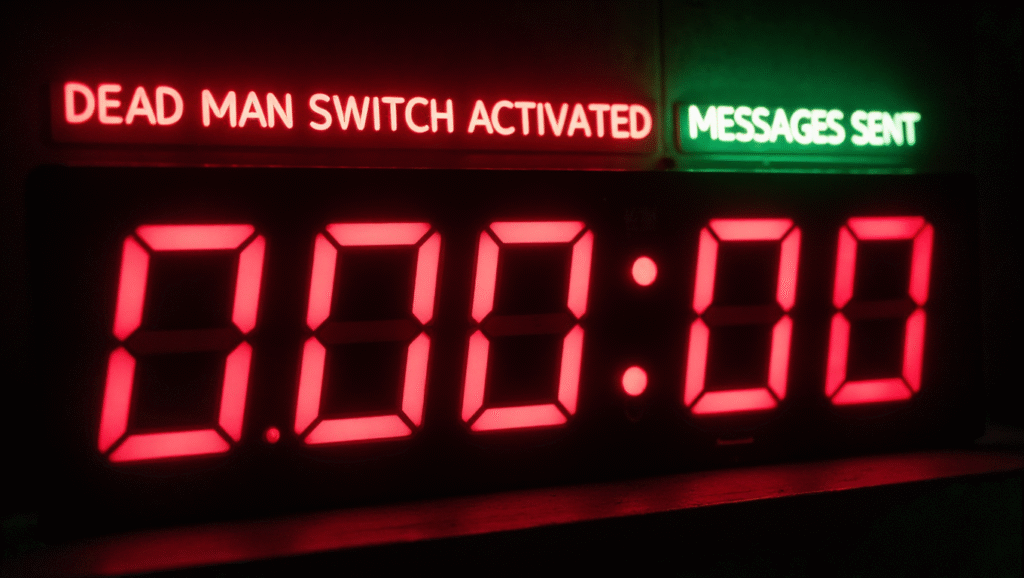
Dead Man Switch (DMS)
- If you stop checking in, your encrypted vault can automatically send itself to trusted contacts.
- Peace of mind for journalists, whistleblowers, and anyone with valuable information.
- Fully testable so you know it will work when it matters most.
Secure Drive
- Convert any USB drive into a self‑contained encrypted vault.
- If stolen, it’s just random encrypted data — useless without your password.
- Portable and secure — carry your secrets anywhere.
Secure Messenger Sender
- Send large files securely via email.
- Automatic encryption, compression, and 10 wrong passwords it self‑destruct.
- Works with Gmail, Outlook, Yahoo, and more.
IMPORTANT — READ BEFORE BUYING
- If you forget your password, your data is permanently locked.
- If you lose your Stealth Lock installation due to PC failure or upgrade, only your original copy can unlock your vaults. You must create restore point on your PC to protect your original Stealth Lock.
- We cannot recover lost data — your security is your responsibility.
- Create a restore point on your PC upon installation.
Why Stealth Lock Is Different
- No backdoors — we can’t unlock your data, and neither can anyone else.
- Local-first security — no “cloud vulnerabilities.”
- Test mode for every feature so you know it works before you need it.
- One-time purchase — no monthly fees, no subscriptions.
💬 Who Uses Stealth Lock?
- Investigative journalists protecting sensitive sources.
- Businesses guarding intellectual property.
- Individuals securing family records, legal files, and private communications.
- Anyone who understands the value of true privacy.
Take Control Today
Once your data is gone, it’s gone. Once it’s stolen, it’s too late.
With Stealth Lock, you take control — and never give it back.
Stealth Lock — Your Data. Your Control. Forever.
Stop trusting the cloud.
Stop giving away your privacy.
Encrypt everything — Vaults, USB drives, even your email.
If you lose your password, nobody can unlock it. Not hackers. Not the government. Not even us.
Protect your files.
Arm your Dead Man Switch.
Send secure messages.
Sleep at night knowing your secrets are truly yours.
Stealth Lock — When Privacy Isn’t Negotiable.
“Stealth Lock — Privacy You Can Take to the Grave.”
Military-Grade Security Meets Stealth Precision
StealthLock applications are engineered with a multi-layered defense architecture designed to neutralize unauthorized access before it begins.
Every installation is fortified with embedded countermeasures, runtime verification, and real-time defense logic — ensuring your security can never be bypassed, cloned, or reverse-engineered.
This is more than protection.
It’s digital immunity.
Tamper-Resistant Execution
Self-validating executables automatically terminate if moved, copied, modified, sandboxed, or manipulated in any way.
Only the original authorized instance can run — anything else is instantly shut down.
Encrypted Core Engine
The heart of StealthLock operates from an encrypted container that only decrypts in memory at runtime.
Nothing touches the disk.
Nothing remains for forensics, malware, or forensic tools to analyze.
Your logic stays concealed.
Always.
🛡 Real-Time Threat Detection
StealthLock actively scans for:
- Debuggers
- Reverse-engineering tools
- Memory inspection
- Virtualization traps
- Sandbox analysis
On detection, the system self-terminates instantly, protecting your data and shielding internal operations.
Secure Configuration Encapsulation
All runtime parameters, keys, and configurations are:
- Encrypted
- Integrity-verified
- Protected from external read/write access
This prevents tampering, unauthorized modifications, and configuration leaks at every stage.
Anti-Cloning Enforcement
Each installation is cryptographically bound to a single device — stopping duplicates or unauthorized copies from functioning elsewhere.
One installation. One device. Zero exceptions.
No Backdoors. No Tampering. No Second Chances.
StealthLock does not weaken itself for convenience, corporations, or governments.
There are no reset codes, no override access, and no hidden master keys.
Your security remains absolute.
Your protection remains unbroken.
This Isn’t Just Security — It’s Digital Immunity.
StealthLock doesn’t simply defend your data —
it eliminates threats before they even form.